
Best Practices for MacOS Logging & Monitoring
Organizations can pull the right logs to manage MacOS platforms in a variety of ways, including using endpoint detection and response (EDR) tools, integrating within Active Directory (AD) or leveraging a Mac management platform like Jamf. From there,
it’s a matter of specifying the logs you want and sending them to your SIEM. This piece details the options and shows you how to build an optimal MacOS logging and monitoring capability.
Challenges of MacOS Logging
Local system logging in the MacOS world is a challenging endeavor due to a variety of reasons.
First, Microsoft is still the center of the enterprise computing landscape, and most organizations either don’t allow Macs or turn a blind eye to their use.
Second, Apple has typically been consumer-focused, so in cases like this, its solutions don’t quite fit the needs of the enterprise. That said, MacOS is an excellent operating system, and getting what you need is usually possible.
Choosing a MacOS Logging Method
A few years back, Apple rewrote the entire logging engine on its MacOS platform and retitled it unified logging. Unified logging normalizes the log engines across Apple’s iOS and MacOS platforms. This caused changes to every aspect of logging, including
creating logs, storing logs and using logs.
One key change is that Mac converted all its log storage to a format called .tracev3, which is a compressed binary format. This means you must use native tools to get the logs back out. Also, you can’t write simple scripts to just copy certain log
files off the underlying Unix file system.
There are a few different approaches to consider when trying to figure out how to get the appropriate logs to monitor:
EDR: The first, and perhaps easiest approach is to look at the capabilities of your EDR tools. Tools such as CylanceOPTICS and CrowdStrike have extensive cross-platform telemetry monitoring and logging capabilities that may be able to get most of this
data quite easily. Those systems will often already be integrated with your SIEM solutions, easing the implementation burden.
AD: Another option is to explore integrating your Mac population into AD, so you can log any network logon events by default through the standard AD integration.
Mac management platforms: These provide another option for gathering and shipping log data from your fleet of systems. Jamf (aka Casper) is the de facto standard here, and it includes features similar to Microsoft System Center Configuration Manager (SCCM).
Jamf offers an enterprise log management framework for shipping logs to your SIEM. You must define specific predicates (i.e., queries) to filter down the stream of events to ship. (Beware shipping all events, because there is an extraordinary amount of
logs with no apparent value.)
Choose What to Monitor in MacOS
Once you’ve got a solution to actually get the logs out, try to identify the specific logs you care about seeing. Consider a dedicated work effort with your Mac management team to pinpoint exactly the logs to search for.
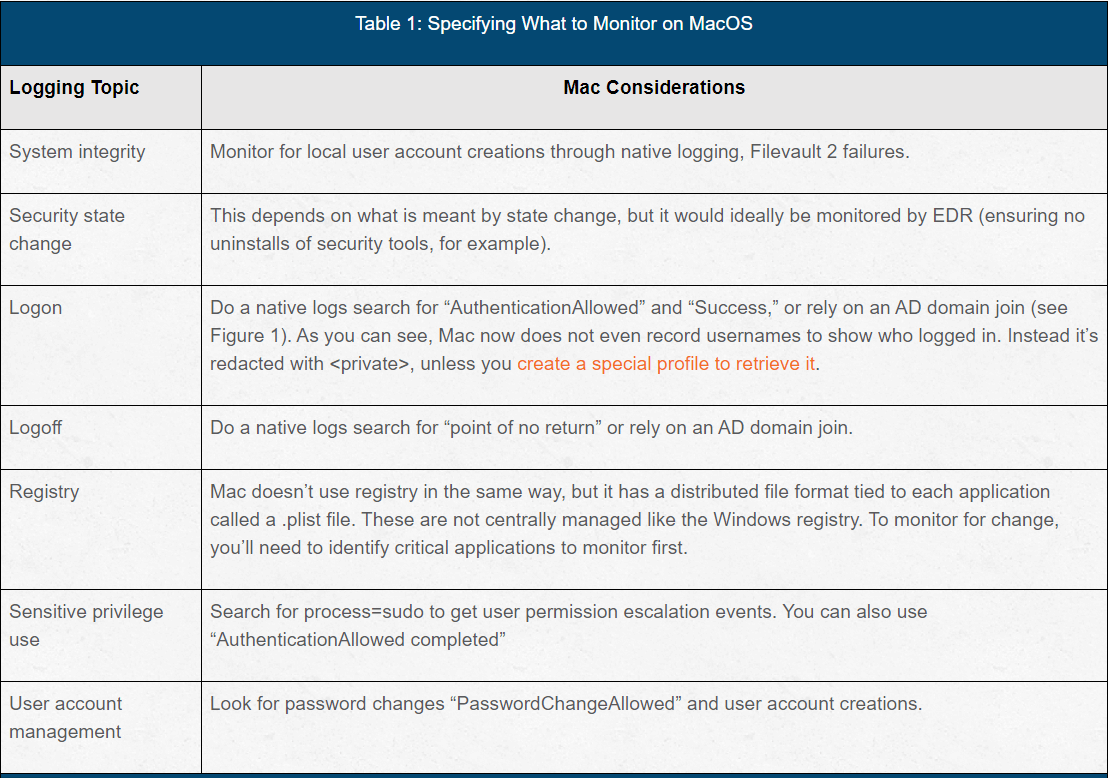
Specific logs can be loosely attributed to a few different key items (see Table 1).
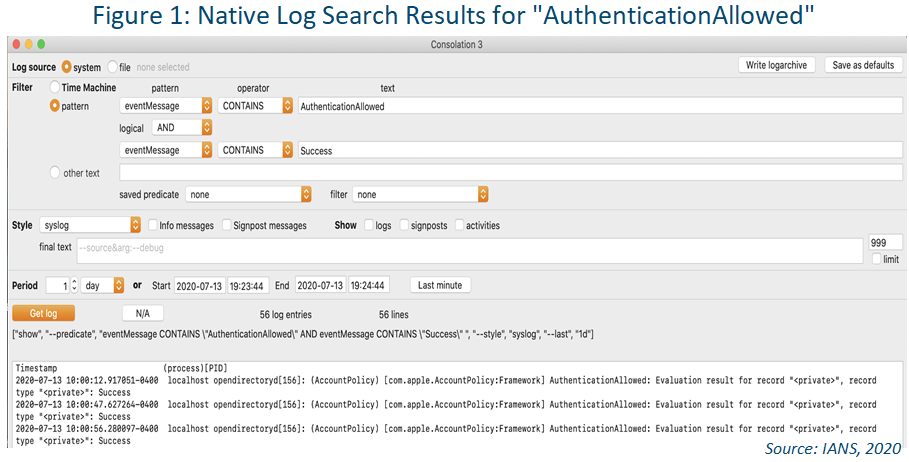
Identifying the logs you want to track can be done with a log viewer like Consolation 3 (shown in Figure 1). Use its user interface (UI) to define search criteria and review and tune the results. Then, take the “predicate” generated at the
bottom and use that in your log shipping solution to pluck those logs from the log stream and send them to your logging solution.
Logging Solution for MacOS
There is no dedicated, one-size-fits-all logging solution for MacOS that directly correlates to traditional Windows logging. To get a workable solution in place:
Be systematic: Apple has highly verbose logs, but they can be culled down through a dedicated process.
Realize you can’t set it and forget it: Apple’s logging standards should be considered subject to change as they don't typically have the longevity of Windows logs. Expect logging standard to change and also anticipate maintenance with each OS upgrade.
Although reasonable efforts will be made to ensure the completeness and accuracy of the information contained in our blog posts, no liability can be accepted by IANS or our Faculty members for the results of any actions taken by individuals or firms in connection with such information, opinions, or advice.